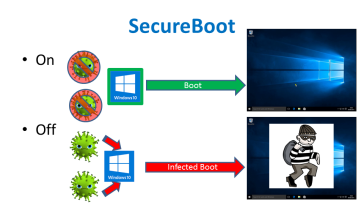
For a long time now, viruses have been a major concern for computer users. You not only risk losing your data, you also risk having your privacy compromised when attacked by Viruses and Malware. Microsoft Secure Boot is a component of Microsoft’s Windows 8 operating system that relies on the UEFI specification’s secure boot functionality to help prevent malicious software applications and “unauthorized” operating systems from loading during the system start-up process.
Although having it activated will make it difficult to install Linux or other operating systems on the computer, the secure boot functionality in is primarily designed to protect users from rootkits and other low-level malware attacks by blocking unauthorized activities and drivers from being loaded during the start up process. Modern computers come with the feature enabled.
This is a platform feature in UEFI, which replaces the traditional PC BIOS.
How Secure Boot Secures Your PC’s Boot Process
A traditional BIOS will boot any software. When you boot your PC, it checks the hardware devices according to the boot order you’ve configured, and attempts to boot from them. Typical PCs will normally find and boot the Windows boot loader, which goes on to boot the full Windows operating system. If using Linux, the BIOS will find and boot the GRUB boot loader, which most Linux distributions use.
With the kind of set up, it is very possible for malware, such as a rootkit, to replace your boot loader during the both process. The rootkit could load your normal operating system with no indication anything was wrong, staying completely invisible and undetectable on your system. The BIOS doesn’t know the difference between malware and a trusted boot loader, it just boots whatever it finds.
Secure Boot is designed to stop this scenario. UEFI will check the boot loader before launching it and ensure it’s signed by Microsoft. If a rootkit or another piece of malware does replace your boot loader or tamper with it, UEFI won’t allow it to boot. This prevents malware from hijacking your boot process and hiding itself from your operating system.
Related Article: A quick guide of switching from windows to linux
How Microsoft Allows Linux Distributions to Boot with Secure Boot
This feature is designed to protect against malware. Microsoft therefore offers a way to help Linux distributions boot. Some modern Linux distributions–like Ubuntu and Fedora work on modern PCs, even with Secure Boot enabled. Linux distributions are required to pay a one-time fee of $99 to access the Microsoft portal, where they can apply to have their boot loaders signed.
Linux distributions then have a “shim” signed. The shim is a small boot loader that simply boots the Linux distributions main GRUB boot loader.
The Microsoft-signed shim checks to make sure it’s booting a boot loader signed by the Linux distribution, and then the Linux distribution boots normally.
Ubuntu, Fedora, Red Hat Enterprise Linux, and openSUSE currently support Secure Boot, and work without any problems on modern hardware devices.
How to Disable Secure Boot
You can control Secure Boot from your PC’s UEFI firmware, which is like the BIOS in older PCs.
You can do this by simply heading to the UEFI firmware and disable it entirely. The UEFI firmware won’t check to ensure you’re running a signed boot loader, and anything will boot. You can boot any Linux distribution or even install Windows 7, which doesn’t support Secure Boot.
Windows 8 and 10 will work fine, you’ll just lose the security advantages of having Secure Boot protect your boot process.
You can can also further control which signing certificates Secure Boot offers. You’re free to both install new certificates and remove existing certificates. If you ran Linux on your PC for example, you could choose to remove Microsoft’s certificates and install the organization’s own certificate in its place. Your PC would then only boot boot loaders approved and signed by you.
What Microsoft Requires of PC Manufacturers
Microsoft wants PC Manufacturers to enable secure boot but in a specific way.
For Windows 8 PCs, manufacturers have to give the consumer a way to turn Secure Boot off. Microsoft required PC manufacturers to put a Secure Boot kill switch in users’ hands.
For Windows 10 PCs, manufacturers can choose to enable Secure Boot and not give users a way to turn it off. This hasn’t been operational perhaps because no PC manufacturer wants to make the only line of laptops you can’t install Linux on.
For now, at least, mainstream Windows PCs should allow you to disable Secure Boot if you like, and they should boot Linux distributions that have been signed by Microsoft even if you don’t disable Secure Boot.
Secure boot is a good tool if you use Microsoft operating system and haven’t thought of using Linux anytime soon. In case you use Linux, you can disable secure boot so that you can use your PC without any tweaks.
Are you using this tool? Have you used it before? Share your experiences in the comments section below.