Our devices and computers normally contain various types of files. The internet also contains various types of files that can be downloaded. You should, however, be cautious about the types of files in your devices and what types of files you download. These files are normally identified by their file extensions.
What Is A File Extension?
This is a string of characters attached to a filename usually preceded by a full stop and indicating the format of the file. The extension indicates a characteristic of the file contents or its intended use. It helps an operating system, like Windows or macOS, determine which program on your computer the file is associated with.
File extensions are different from file formats in that, a file extension is just the characters that appear after the period, while the file format is the type of file. For example, in the file dignited.docx, .docx is the file extension while the file format is a Microsoft word document.
.EXE
This is an executable program file. Most of the applications running on Windows are .exe files. Its popularity among users, importance to the Windows file system, and ease-of-use makes it the best choice for a malware attack. One of the most common methods of delivery is through an email attachment that executes a virus when you open the file.
.BAT
This file contains a list of commands that will be run on your computer if you open it. These types of files were originally used by MS-DOS. The mere fact that the commands run when the file is opened makes such files a good option for malicious programmers.
.SCF
This is a Windows Explorer command file and can be used to tell Windows Explorer to execute commands that are dangerous to your computer.
.COM
This is the original type of program used by MS-DOS. It is saved in a binary format and is similar to an EXE file. It is commonly used for executing a set of instructions. If it contains malware and is opened, the instructions will be executed causing harm to your computer.
.CMD
This is a batch file similar to .BAT, but is run by CMD.EXE instead of COMMAND.COM. This file extension was introduced in Windows NT but it can also be run by DOS.
It is a popular file type for writing malware. It may be used to delete data in a directory or replicate itself and open a program repeatedly to deplete a computer’s resources, which slows down and crashes the system.
Related Article: All you need to know about Malware
Other File Extensions to Be cautious about
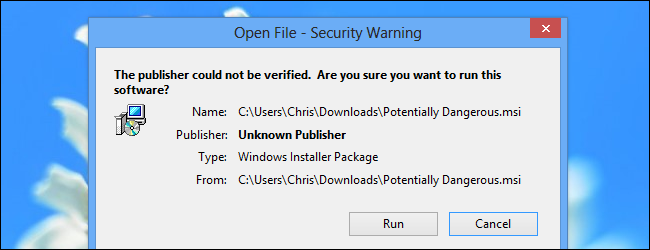
.MSI: This is a Windows installer package that contains installation information for a particular installer. It is mostly used for Windows updates and third-party software installers.
.VB/ .VBS: They contain code that can be executed within Windows or Internet Explorer via the Windows-based script host (Wscript.exe). This file type is associated with many viruses and malware. They are often delivered as an unknown e-mail attachment that will run when opened.
.PIF: A .PIF file contains information that defines how an MS-DOS-based program should run. Such a file can be used to transmit viruses or other harmful scripts.
.HTML: HTML is the standard language used to create web pages. In this format, trojans and worms can be hidden easily
.ZIP: This is the most popular way to pack multiple files into a single digital package. Hackers can package various viruses in such files.
How to avoid Malware hidden in files
- Have an up to date antivirus software which will help you stop infected files.
- Block automatic file execution or manual launching of unapproved executables.
- Always make sure that the attachment really came from the person or institution that seemingly sent it.
Many computer viruses are spread via email attachments and other files that may come through flash disks and other external devices. It is important for you to be vigilant about the types of files you have on your device.
Discover more from Dignited
Subscribe to get the latest posts sent to your email.












